The phenomenon of unsolicited and unwanted messaging dates back to the earliest communication platforms: from prehistoric cave graffiti and postal chain letters to popup ads and robocalls. To prevent spam, most online services rely on large-scale inspection of plaintext conversation content or detailed social-graph analysis to determine who is saying what to whom and whether or not that should be allowed. At Signal, we build on a foundation of privacy and do not have access to that type of data or metadata.
We build Signal in the open, with publicly available source code for our applications and servers. To keep Signal a free global communication service without spam, we must depart from our totally-open posture and develop one piece of the server in private: a system for detecting and disrupting spam campaigns. Unlike encryption protocols, which are designed to be provably secure even if everyone knows how they work, spam detection is an ongoing chore for which there is no concrete resolution and for which transparency is a major disadvantage. If we put this code on the Internet alongside everything else, spammers would just read it and adjust their tactics to gain an advantage in the cat-and-mouse game of keeping spam off the network. The Signal protocols, cryptography, and source code are peer reviewed, shared for independent inspection, and provably private by design. We are bound by these security guarantees, so that your conversations and contacts remain as private and protected as ever, even if we keep spam-fighting tools out of sight.
The worldwide community of people using Signal has grown dramatically this year, and that growth has made Signal a more attractive target for enterprising scammers. We’ve been making adjustments to keep the Signal network free of spam, through minor changes to our client applications and with new server software to detect and disrupt spammers. Fighting spam without message content or social graphs is challenging, but we do so in a way that is in line with Signal’s commitment to privacy.
Modifications to Message Requests
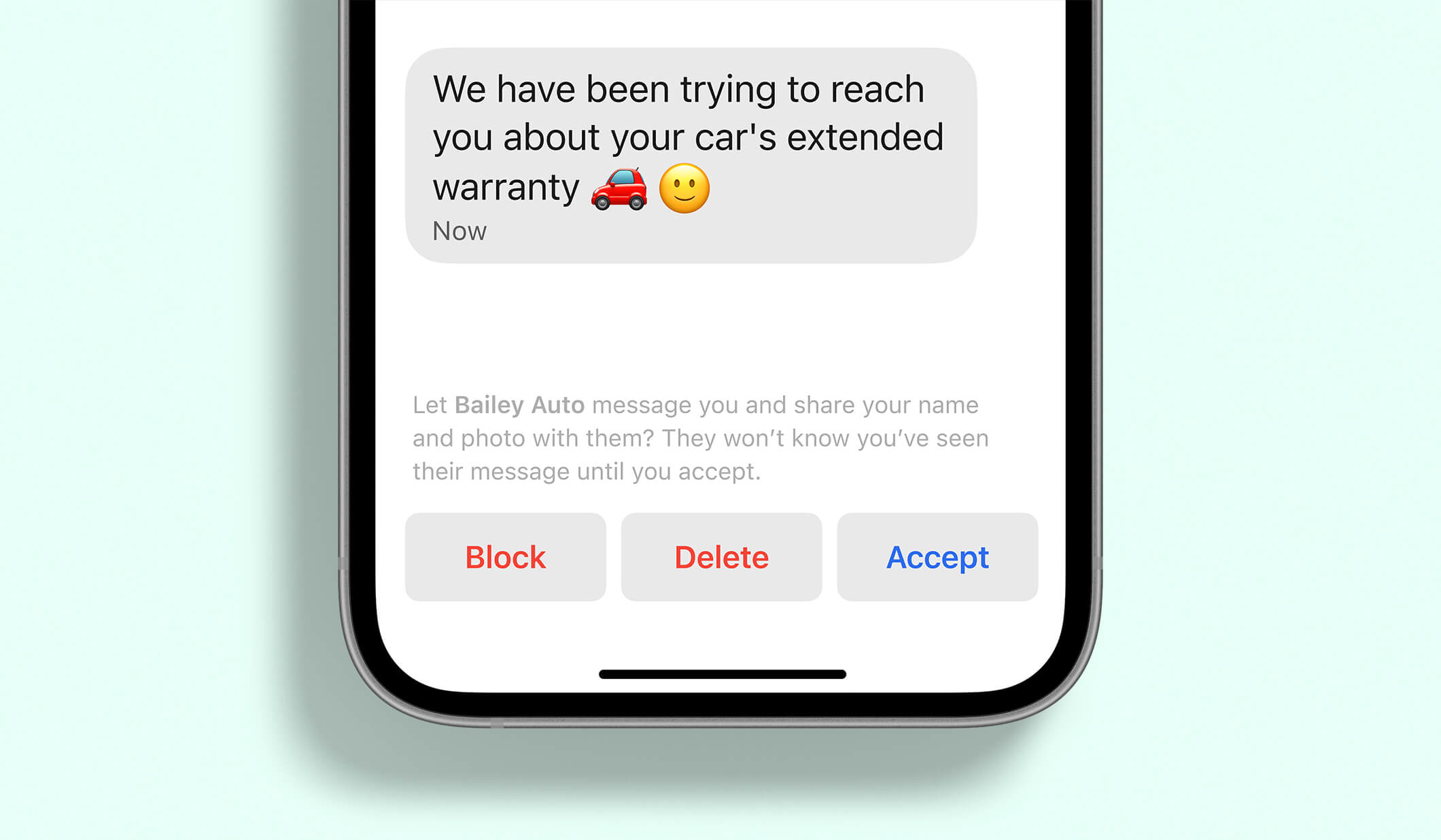
In the earliest versions of Signal, every message delivered to your account was given equal treatment in your inbox. Family members, lifelong friends, and enterprising scam artists could all occupy the same space in your conversation list. We introduced message requests so you can quickly see more contextual information before accepting, deleting, or blocking messages from someone who isn’t in your local address book.
As more people signed up for Signal, more people wrote into our support team about receiving random spammy message requests. Attractive Young Singles In Their Area were initiating conversations using provocative profile photos in an attempt to lure people into scam traps. Signal profile photos and profile information are end-to-end encrypted, just like your conversations. To prevent misleading images from imitating your bank or future romantic partners, we now blur profile pictures for all conversations initiated by senders outside your address book until you tap on the photo.
Scammers are often motivated to get you off of one platform and over to their fake website for phishing or other fraud. To eliminate an easy way for scammers to get people to click on questionable links, we modified the Signal apps to stop linkifying URLs rendered on the message request screen.
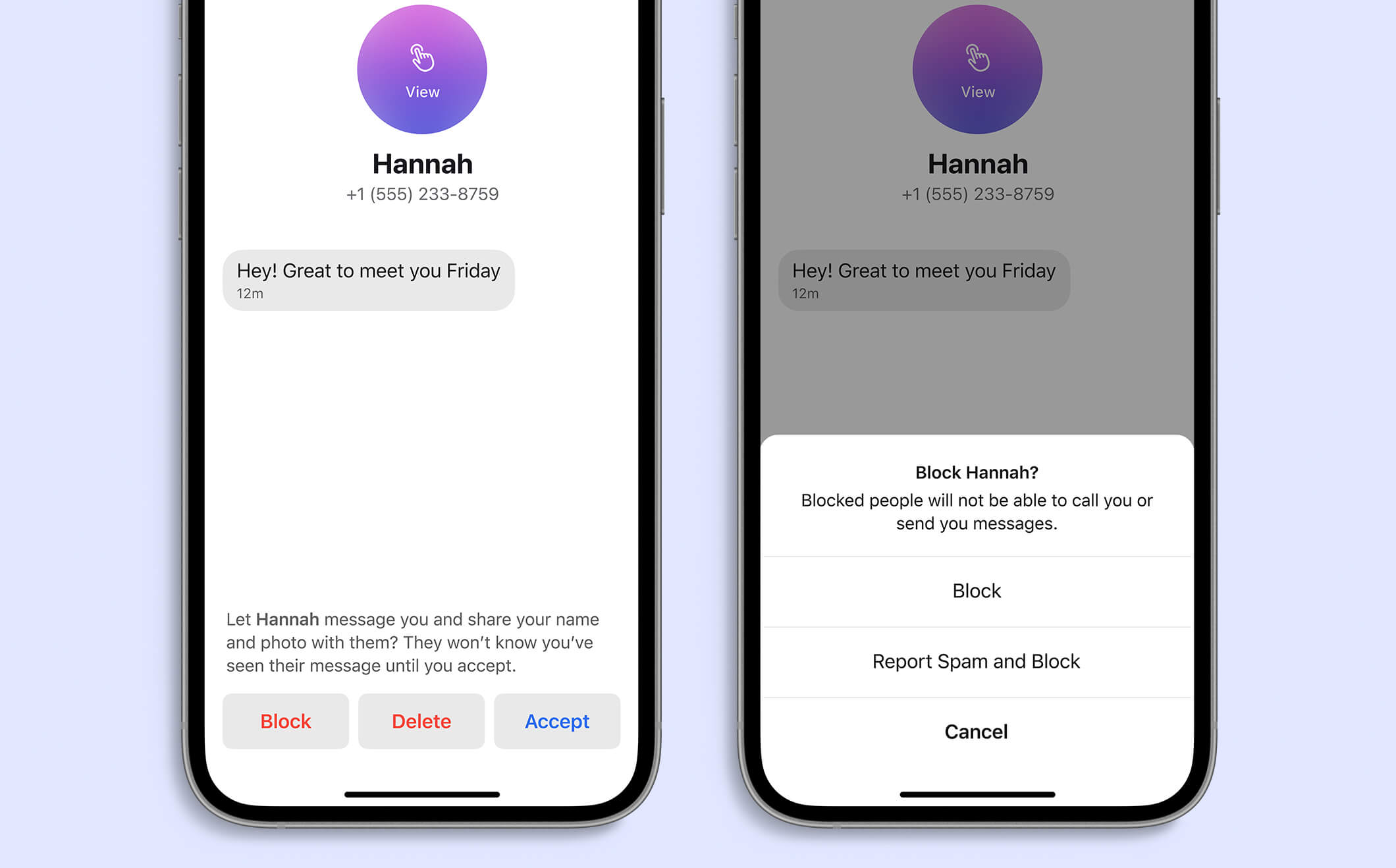
These minor UX modifications make individual spam messages less effective, but to squash out spam across the network, we added recourse for recipients if an unwanted inbound message appears. When you block a user from the message request screen, you can also report the message as spam. Other services may use this as an opportunity to collect unencrypted conversation content or to upload additional information used to identify spam campaigns. Signal is committed to your privacy, and does not do this, so we take a different approach.
Server Code and Spam Fighting
Signal is designed from the protocol level on upwards such that client applications do not trust the server that is delivering end-to-end encrypted content. The server-side inspection that other platforms use to filter unwanted messages is not possible on Signal because we build our systems so nobody – not even Signal – can read your messages or know who your contacts are. We make all of that client code, library code, and server code public for contributions and reviews. In a system without insight into message content, we rely on messaging behavior to enforce limits on the service.
When a user clicks “Report Spam and Block”, their device sends only the phone number that initiated the conversation and a one-time anonymous message ID to the server. When accounts are repeatedly reported as spam or network traffic appears to be automated, we can issue “proof of humanity” checks to suspicious senders so they can’t send more messages until they’ve completed a challenge. For example, if you exceed a configured server-side threshold for making requests to Signal, you may need to complete a CAPTCHA within the Signal application before making more requests. This approach slows down spammers while allowing regular messages to continue to flow.
As our spam-fighting capabilities expand, so does the complexity and size of our spam-specific software. To prevent spam on Signal, we need to build this spam-battling logic in a separate server component. The interfaces to this code will be public, but the implementation will not be shared. We’re working hard to keep the amount of non-public code as small as we possibly can, and all other parts of the server software and all of its interactions with spam-fighting code remain available in the open. Keeping this small piece of software private helps us stay one step ahead of spammers and doesn’t change the fundamentals of Signal’s security model.
Less Spam, Same Security
What you say on Signal remains private between you and your intended recipients, as it always has been. With some small UX changes to the client applications and a small new private piece of spam-fighting server code, your private conversations can remain between the people you want to talk to, and not with dubious royalty trying to transfer their inheritance to an offshore banking account.